We’re often taught to reject complexity, and there’s a certain simple, elegant logic to that idea. Taken at face value,…
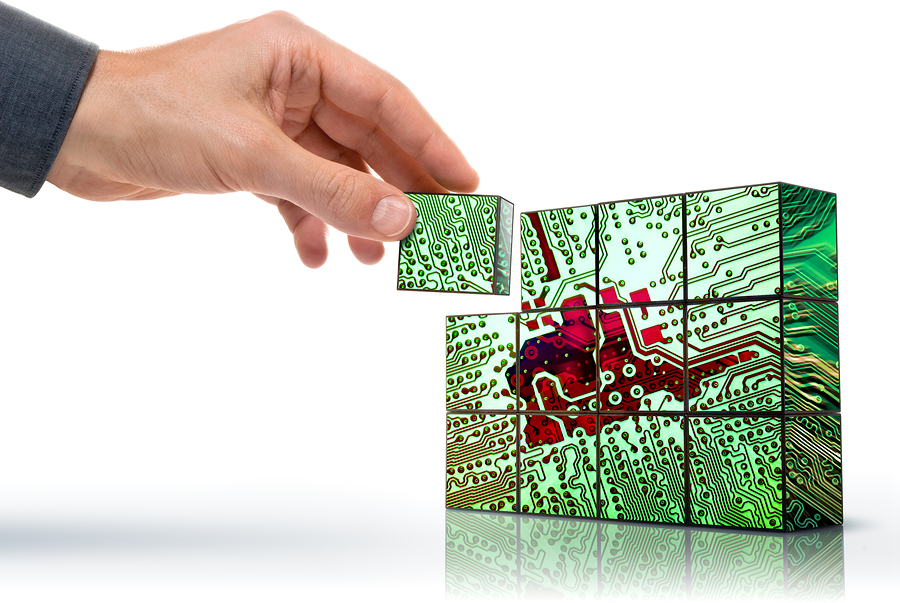
If you’re approaching NetWorker for the very first time, it might seem a little intimidating. There are a lot of…
“Oxford economics historian Avner Offer believes that we’re hopelessly myopic. When left to our own devices, we’ll choose what’s nice…
At Dell Technologies world, PowerProtect was announced. This is next generation data protection software and appliances; these aren’t just an…
Do you want a backup system, or a staging system? This might seem like an odd question, but I’m asking…
“Oxford economics historian Avner Offer believes that we’re hopelessly myopic. When left to our own devices, we’ll choose what’s nice…
And there she lullèd me asleep, And there I dreamed—Ah! woe betide!— The latest dream I ever dreamt On the…
Databases. They’re expensive, aren’t they? What if I sold you a Dangerbase instead? What’s a dangerbase!? I’m glad you asked. A dangerbase…
There was a time, comparatively not that long ago, when the biggest governing factor in LAN capacity for a datacentre was…
The NetWorker usage report for 2016 is now complete and available here. Per previous years surveys, the survey ran from December…