PowerProtect Data Manager version 19.21, and 19.22 are out. 19.21 came out in September, but I confess I’ve been spectacularly…
PowerProtect Data Manager 19.20 was released in June, and now that I’ve got a few minutes to spare I wanted…
Data Manager 19.19 came out at the end of March, so I’m a little late writing about it: I’ve been on…
The last few months have been a pain for me. And I don’t mean “oh it’s been busy” (well, it…
Yesterday morning over breakfast, I was reading the excellent article, Mastering Assumption Testing in Product Management, and I was struck…
It’s raining bookmarks A few years ago I dived back into having a central, multi-platform/multi-browser bookmark manager and since the…
PowerProtect Data Manager features a powerful access control mechanism which allows you to isolate users of the system to only…
A few days ago I passed my three year milestone in product management, and that seems like a good point…
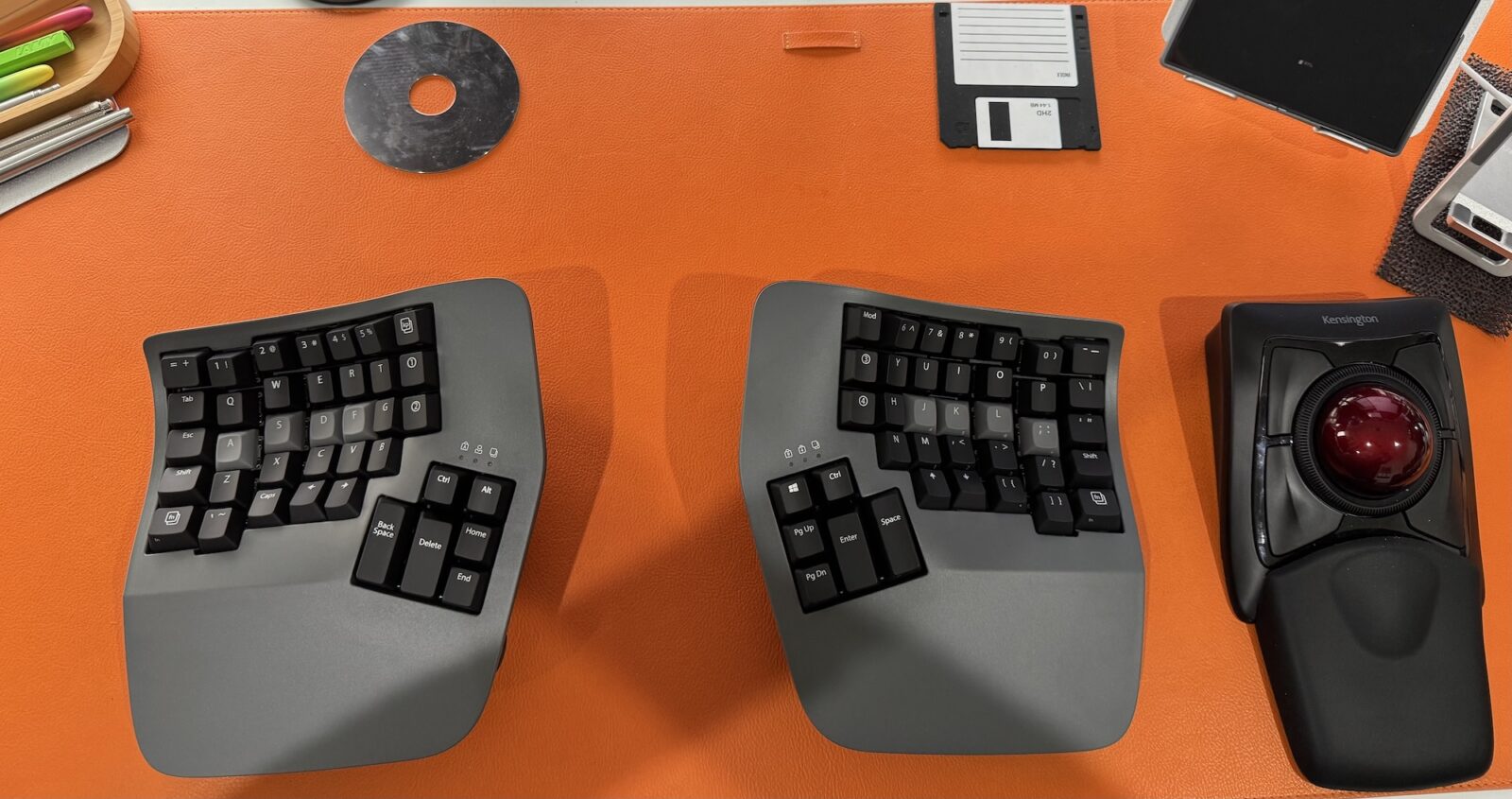
Of Tennis Elbow and Forced Downtime I’m on my final day of three weeks off. I had sort of aimed…
On the 31st of December 2024 I find myself reflecting on the year that was, and I’m reminded of an…